Fraud Intelligence
Fraud prevention is a constant arms race. Rule-based systems aren't enough. We build AI systems that adapt to new attack patterns and cut false positives, improving the user experience while protecting your bottom line.

Real-time Transaction Scoring
Sub-ms scoring latency pipeline
Score thousands of transactions in under 200 ms. Fast enough to block fraudulent card-not-present (CNP) or digital wallet transfers in-line.
Multi-dimensional scoring model
Risk rules, device identity, IP velocity, and global blacklist variables are evaluated in real time, assigning a risk score giving the models zero day detection across global attacks.
False Positive and decline rate optimization
Smooth sliders and threshold simulations test the impacts of custom rules against historical data to ensure dropping bad transactions won’t drive buyers off your platform with false declines.

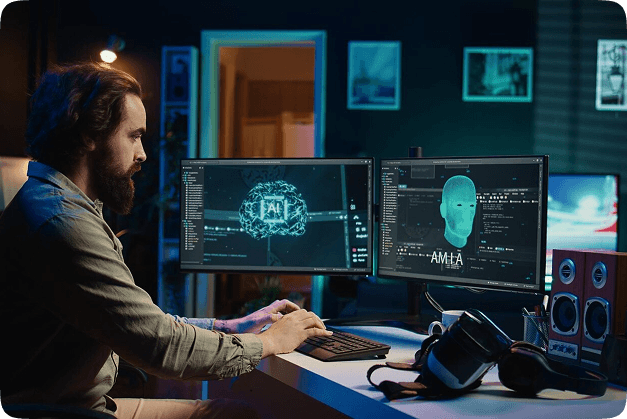
Machine Learning Model Management
Custom model trained on your data
The platform you are training on your transaction history. Models spread cross-train online network patterns, meaning they figure out how to block by themselves.
Model performance monitoring and drift detection
Evaluates latest alerts performance with visual dashboards, rich UIs, and alerts the team with anomalies so models can adapt and update a new set of data set on the model self-training.
Team collaboration workflow tools
Accept ML lifecycles to trigger business and IT team closed-loop alerts, managing a small fraud model updates precisely impacting the existing business requirements in tech.

Account Takeover and Identity Fraud Prevention
Behavioral biometrics anomalies AI signals
User attributes such as typing cadence, mouse jitter, and app-swipes verify the legitimate users are operating their device. Up-front alerts trigger step-up multi-factor (MFA) to block ATO before execution.
IP/Device fingerprinting
Deep proxy and VPN checks on device network layer pinpoint the exact root systems that rely up to switch devices between accounts.
Test/Guest checks detection bypass
Look block bots and check proxy BINS and blocks they’re actively crawling the online apps, opening virtual accounts, and registering the lists for spoofed accounts, open the bots in shadow mode.
